Circuit Fingerprinting Attacks: Passive Deanonymization of Tor Hidden Services
We can do this from the command line by typing the following. Hydra is listed as a Wayaway Partner on the forum’s footer along with Hydra logos, market links, and various digital advertising scattered across the forum. If you wanna lose your money, give it to Nemesis. Their forum is currently filled with mostly advertisements spam, not super good. We’re a place where coders share, stay up to date and grow their careers. Subscribe to rss feed. If you decide to set up a Tor relay, or to add a Tor hidden service, you would configure those through Vidalia. Especially the fact that Russian speaking countries make up a massive part of the dark web population made this even more visible. Digital records from online marketplaces offer a unique opportunity to investigate crime displacement, allowing us to pinpoint where crime moves to and the pathways it takes to get there. You can follow him at @kylerankin. Although blockchain provides anonymity for the wallet owner, the fact that crypto wallets are traceable assets can damage this anonymity. And refill with metal.
Accessing Darknet Markets via the Tor Network
The dark web is a hidden network hosting. Printing this content is for the sole use of the Authorised User named subscriber, as outlined in our terms and conditions. Ulbricht was eventually arrested by US law enforcement and Silk Road was seized and taken offline. «We know there are 100 live onion sites that are part of the active criminal underground as either high tier criminal forums, lower tier but still explicitly criminal forums, or dark web market where illegal goods are sold,» he said. I looked forward to delivery day, tracking the package through FedEx, and getting my reusable produce bags ready. More often they are simply extortion attempts. In late 2014 this successor site met its demise as well, in another law enforcement sting called Operation Onymous, at which point Evolution and Agora took up the baton. Compared to equities and many other assets, crypto has had a relatively short history. Use alternative Nemesis Market Link emails. Structural covariates test whether properties of the network itself impact the probability any pair of nodes will have a network tie and the intensity of that tie. Experts on both the deep web and the surface web provide insights from IT, research and monitoring, law enforcement and drug user perspectives. NordVPN is my personal recommendation. This will take you to the account creation page.
Get the latest insights in your inbox
Ranks for ONION in different categories calculated by market cap : Mineable Coins 151, Privacy Coins 22. Whatever drugs, illicit drugs are available, they’re probably being sold on the darknet. Only then will Faire’s hypocrisy end, where they say they love the makers via high customer service, but all the while they control and take what they want from them consistent, very high commissions. Monopoly market platform was designed to prevent vendor exit scams and phishing attacks against its main URL. Used in with a dedicated private browser, DuckDuckGo is a powerful search engine and a potent privacy tool. We do not support or encourage buying/selling illegal goods on dark web markets. The European Monitoring Centre for Drugs and Drug Addiction EMCDDA is the leading authority on illicit drugs in the European Union. Web crawlers that build the indexes used by conventional search sites do not crawl the dark web. Your email address will not be published. Fresh Onions is an open source TOR spider / hidden service onion crawler hosted at zlal32teyptf4tvi. The econometric estimations are used for exports and imports functions, household’s consumption, savings and investment choices, and firms’ pricing and production behaviour, including the choice of ordinary production factors physical capital, high skilled and low skilled labour, energy and other intermediate consumptions. Police crackdowns, as is the case for traditional drug markets, are not effective measures to lower the volume of sales on online illicit drug markets. In the model, the behaviour of economic agents is based on the determination of optimal, or desired values. 5%, while on the weekly chart, the token has slight gains of about 1. This approach was adopted from analyses of human migration networks to control for countries of different sizes Vogtle and Windzio 2016. «The success of this operation again shows that international cooperation is essential in combating crime on the dark web. We’d love to hear from you. However, the likelihood of approval for those products based around the alternative crypto asset is similarly unclear. 449 and the clustering coefficient to 0. All in all, over 10 Bitcoin spot applications have been filed, with all of them still awaiting approval by the Securities and Exchange Commission SEC. Please turn this functionality on or check if you have another program set to block cookies. Besides, DWMs may not only appear as drug markets but can also be interpreted as nesting spots for cyber threats. Detailed TOC of Global Dark Web Intelligence Market Research Report 2024. Please note that in the annex 4 of the impact assessment report, the general description of the model available in MIDAS has to be complemented with the specific information on how the model has been applied in the impact assessment. Based on this, studies analyzed the total size of the Tor darknet or the dark web , categorized the content of the websites , examined the links of the individual websites among each other or investigated the popularity of onion services. It makes up for this with enhanced security and user safety features, helping users to ensure they are not getting phished.
Creekorful / bathyscaphe
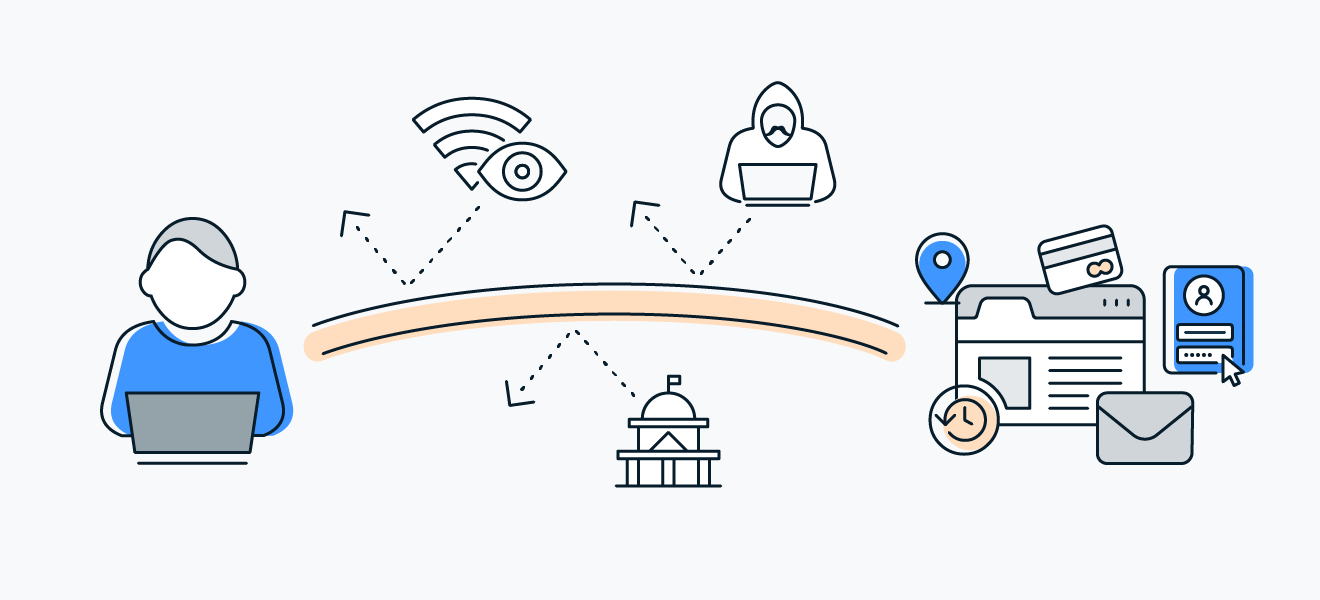
In light of recent busts, however, dark web operators have increased their vigilance and are scrutinizing applicants more thoroughly. The website addresses and computer servers hosting these websites were seized yesterday as part of a coordinated international law enforcement action involving the Justice Department’s Criminal Division, U. «For instance, when users connect to the onion services. Cryptomarket participants have been shown to have a minimal reaction, or one that is temporary, to overtly large shows of force and to have the ability to adapt through displacement techniques. I’ve been leaning into them a lot recently see above meatless nonsense but I’ve never had them in anything sugary. No relationship is created with you, nor any duty of care assumed to you, when you use this blog. However, this partnership faced opposition from WayAWay and led them to associate itself as Kraken. So, what’s driving that downturn. We use cookies to help provide and enhance our service and tailor content and ads. Arrange a call to discuss a tailored solution or explore our platform for free. For instance, one vendor explained, ‘If I see something that’s a good deal i will buy it just for the sole intention to resell but always bulk listings obviously, that’s how you make money. 11 and the average price of ONION should be around $0. Hurricane Ida dragged crude prices from the one week lows as she entered the Gulf of Mexico and forced both BP and Chevron to cut production and evacuate some staff for safety reasons. Along with Recorded Future, Flashpoint, Digital Shadows and Terbium all have raised millions of dollars in recent years to meet this demand. Remember though, Nemesis Market moderators always have your back in the event of a problem and we always deal with disputes in the fairest manner possible. An interesting feature of Nemesis market is that they show reviews and sales of a vendor from other markets, so buyers can see if a vendor is reputable or not. This could bring in larger traditional investors who previously did not want to touch crypto. This highlights the importance of accurate information in navigating the shadowy corridors of the darknet. Thank you for pointing that out. It defies the norms for listings and their descriptions, thus for the time being, it’s still interesting to look at because it gives vendors more leeway in what they can try to sell for XMR. Get the latest market insights, developments and updates, direct to your inbox.
Quick links
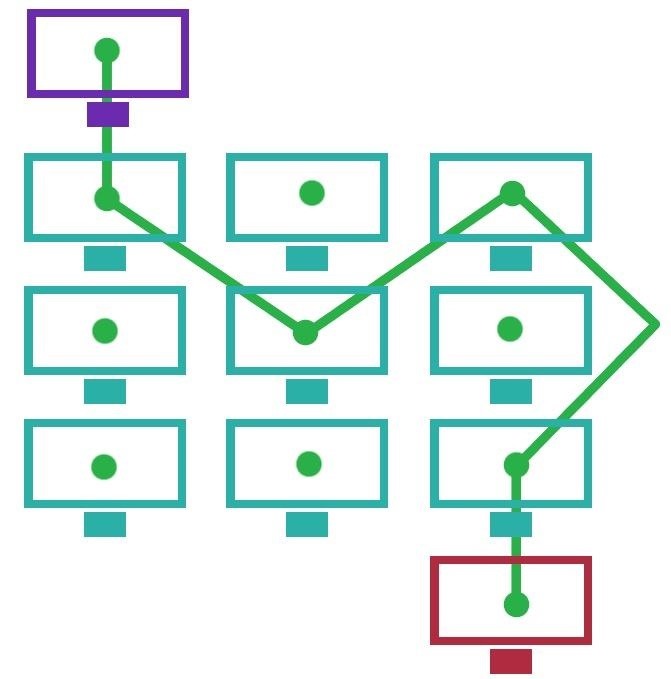
«Our Cyber Crimes Unit once again used their cryptocurrency tracking expertise to help take down this site and identify the criminal behind it. Usually, this involves accessing the web or other Internet services as a client—but a Tor node can also act as an anonymous server. Phan and Prihar communicated on a daily basis to facilitate their criminal enterprise. We’ve compiled an up to date list of the best onion sites in 2023 so you can get a taste of what’s out there. FUCK OFF YOU POOR CUNTS. Additionally, The Report Highlights the Involvement of Numerous Companies and Individual Advisors from Around the World in Establishing Official Economic Ties with The Organization, With A Focus On Type And Applications. Notably, Eclipse relies on 1 the Solana Virtual Machine SVM for transaction execution, 2 Celestia for data availability, 3 Ethereum for settlement security, and 4 RISC Zero for zero knowledge fraud proofs. Overnight, the site was taken down, with law enforcement seizing the servers that hosted the website and arresting the alleged operator of the market. As the dark web continues to evolve or devolve, as Ormsby said the question remains for enterprise CISOs: Should enterprises be taking specific actions regarding the dark web, or is maintaining an overall strong security posture enough. Say you want to anonymously send some tax fraud data to your local newspaper through its SecureDrop. This resource is similar to the surface web’s Wayback Machine. It shows the percentage gains and losses for each time period. E Transfer to Card StripeChequeCash. You can use Dread to learn which dark net markets are reputable and their locations. Select Accept to consent or Reject to decline non essential cookies for this use. The Justice Department announced today a disruption campaign against the Blackcat ransomware group — also known as ALPHV or Noberus — that has targeted the computer networks of more than. We captured listings offering access to online accounts only. Onion sites aren’t inherently dangerous, but they can be. Irrors: Germany, Worldwide, UK, EU. Onion addresses, there is the simple issue of possible number of characters in a. How are they going about this. Notice the variety of merchandise: some of the items are for, shall we say, personnel recreational use while others threaten enterprise security, like the WordPress zero day. Some ISPs and governments take a special interest in anyone they detect using Tor to track potential criminal activity. It is completely anonymous and no one can trace your website location. Today we’re gonna talk about the world without centralised authorities, the world of Tor hidden services. As there are so few gift card for bitcoin services around, Swanson said, the lion’s share of activity in this sector was likely to come from just one or two of its 60,000 retailers, most likely Gyft and e Gifter – the biggest on the market. There’s a lot of advanced cryptographic protocols and processes behind the workings of what I’m about to explain, but for the purpose of keeping this post short and tailored for a wide audience, I’m going to simplify everything as best I can.
National Bureau of Economic Research NBER
Which is in the grips of an overdose crisis. Many cybercriminal entrepreneurs lack the skills and techniques to provision certain parts of their business model, leading them to outsource these parts to specialized criminal vendors. Denying criminals a space to operate freely to conduct their nefarious activities is the first step in stopping this activity from happening altogether. We will change this to /var/lib/tor/hideme/HiddenServicePort tell Tor on which port it should listen and on which port it should forward the request. There were almost three times as many NordVPN accounts than Windscribe, the next most frequently listed VPN service. Find useful infographics and photographic material on the Virtual Power Plant and various aspects of the energy system. Another approach to hidden service scalability is implemented by OnionBalance, a tool that provides load balancing by producing a master descriptor which contains a mix of introduction points from different hidden service instances. Who was a student of whom, using RePEc. Working dark web links 2024 update. New hidden wiki updated for 2023. I suppose an exit could be compromised, but anecdotally that seems unlikely. To view or add a comment, sign in.
Mar 2, 2023
Many thanks to my fellow panelists Michael Reeder Jason Bertoldi, and Collin Cox for their wonderful insights. Get it for PC, Mac, iOS. Publishers indexing in RePEc. Cat /var/lib/tor/hideme/hostname. 2023 screen shot from 0day. Drugula is an agorist marketplace that specializes in the free of state control distribution of psychoactive substances. This is for example the case if an inadequate terminology is used to describe the context of the research e. Litigation Funding Crypto Litigation. And inside the descriptor, there are the introduction points that allow the client to introduce themselves to SecureDrop’s Onion Service. Surprisingly, many of these criminals are not your run of the mill black hat hacker, but brokers registered with the SEC: genuine finance industry professionals – check it out. The behaviour of households. Learn more in our Cookie Policy. Law enforcement, and we will continue to use our sophisticated tools and expertise to dismantle and disable darknet markets. So, you only get to filter for. In April 2012, an undercover special agent claiming to be a drug smuggler who specialized in moving large quantities of illegal drugs, began communicating with Ulbricht, who under anonymity was using the name Dread Pirate Roberts and DPR, about selling illegal drugs on Silk Road. Number of listings refers to the total number of accounts for sale, regardless of whether they are listed separately or together.
Online reviews and high involvement product sales: Evidence from offline sales in the Chinese automobile industry
Dark net links Updated for 2024. Hydra’s money laundering features were so in demand that some users would set up shell vendor accounts for the express purpose of running money through Hydra’s bitcoin wallets as a laundering technique. However, several thousand onion addresses may belong to a single botnet. ProPublica is a non profit, Pulitzer Prize winning news outlet that focuses on abuses of power and issues of public trust. Ten days after UniCC announced its retirement but slightly before the announced closure date, it was reported that Russia’s Federal Security Service FSB had detained the site’s alleged operator: Andrey Sergeevich Novak. There are other vendors that offer dark web monitoring services that cater to consumers. 118th StreetNew York, NY 10027United States212 854 2459 Phone212 854 8059 Fax. Monitor exclusive dark web forums and private hacker channels. They also hide their location, ownership, and other identifiers. Still, they thought western authorities would keep this information private from Russian officials due to the current Russia Ukraine war. They combine tools to ensure anonymity of participants with the delivery of products by mail to enable the development of illicit drug trafficking. «It is a plain fact that criminals use advanced technology to commit their crimes and conceal evidence – and they hide behind international borders so they can stymie law enforcement,» said Assistant Attorney General Caldwell. Silk Road not only aggregated thousands of drug vendors, it created a user friendly interface that resembled a clear net shopping website. Its user friendly interface enhances its accessibility, making it an attractive platform for both new and experienced users. That is, the extent to which vendors from Market A move to Market B also influences whether vendors from Market B move to Market A. Awaiting delivery to update ratings. Wells Fargo, for instance, uses roughly 50 different sources of threat intelligence.
This Feature Is Available To Subscribers Only
VAT registration number 171021261. Recently size and content of Tor hidden services are highly concerned because of emerging illegal content. Their popularity as markets inillicit goods has steadily grown over the years. Our final sample comprises 17 markets, 979 unique vendor aliases, and 221,094 product listings over an approximately 12 week period from 15 November 2020, to 9 February 2021. Congrats, you’ve been granted an access to the exclusive Crypto 101 Handbook. Peter Loshin, in Practical Anonymity, 2013. Halving is when miners, which are entities who uphold the bitcoin network, see the rewards for their work cut in half. Non fungible tokens are high risk assets and have experienced a considerable reduction in trading volume during the crypto winter. The very first post quotes Debians announcement, which makes clear that this is not about hiding or otherwise «protecting» the servers. 999 percent of the time.
Support and Help
Start your NordVPN trial here. Precision Reports stands as a reliable source, offering market reports that furnish the crucial insights necessary for your business to take the lead. There are just over 6000 nodes altogether at the time of writing, run by volunteers. 1 billion in 2021 to $1. However, others argue such hold times can be misused for profit making purposes. This is an invite only market where the items listed for sale are known as «bots. Cryptocurrency exchanges are a popular place for many newcomers to buy their first DeepOnion because they make the buying process very simple But We recommend using cryptocurrency exchanges only for trading—not for storing your DeepOnion. Faire is a reality, and I don’t think it’s going away anytime soon. Generally that service costs around $70. DeepOnion is a hybrid cryptocurrency that uses proof of stake PoS and the X13 proof of work PoW algorithm. The desktop version of the Tor browser can be downloaded directly from the Tor project’s website. Other notable differences included local brands, such as streaming platforms IVI Amediateka being as or even more popular than their international counterparts, such as Netflix. If the address resolves to your server, you’ve successfully hosted a hidden service. The EMCDDA is located at. To understand what DNMs are and how they operate, it’s important to first clarify that there are actually three different layers of the Internet. Servers configured to receive inbound connections only through Tor are called hidden services. Volume of Transaction. Open source darknet market with lightning network payments. Since a v2 address is 16 characters long, the probability to find of a randomly generated active onion address is 2− 65 if there are, for example, 30,000 active onion services. «The seizure of the criminal marketplace, Hydra Market, reflects the effective collaboration of law enforcement to stop criminal enterprises from their illicit activity. Generally, after a purchase is made, the funds are held ‘in escrow’ to be released when the buyer states the seller has met the terms of the purchase.
Blog
Please read the Tor FAQ. The publication adopts an EU focus of what is a global phenomenon. Protect publisher and users of the services against identification. That’s why it’s important to use online security tools that protect your personal data. The investigation of the most requested onion addresses confirmed this. Tested Tor links working in 2024. 000003, and now sits at null. Our easy to use Setup wizard allows you to build a distributed grid for your enterprise in minutes. There are a number of Russian specific forums and bulletin boards across the Darknet. On the subject of the bar, they’ve opted for a low profile espresso setup, so that their staff can focus more on the customer. The continuous intraday market is therefore also called an organized over the counter OTC market. If you get a screen like this, you have successfully configured your Tor hidden service. Scallion uses GPU cracking to generate addresses, while Eschalot works using wordlists. 8, with a subsequent target surpassing $1. By subscribing, you agree to our Privacy Policy and may receive occasional deal communications; you can unsubscribe anytime. Since it became publicly known, the dark web has built a mythology for itself and all the things that may or may not be found there. We have reported and marked them as Spammers. Job openings : NLnet is looking for a Rust developer. Looking for a good book to read. Why on earth would you use a vpn to connect to Tor. All material on this site has been provided by the respective publishers and authors. Within one year, up to 92. Newly registered users cannot view any of this market’s listings though until they deposit at least $50 of Litecoin, Bitcoin, or Ethereum. It doesn’t keep traces of your messages either — everything sent between ZeroBin’s servers stays private.